Zadara Cloud Services Policies¶
Overview¶
Zadara Cloud Services Policies define the permissions for accessing Zadara Cloud Services functionality.
Access to Zadara Cloud Services functionality
Access to Zadara Cloud Services functionality is determined jointly, by two entities:
Zadara Cloud Services Policies, which determine what functionality is permitted. Each policy consists of a list of Zadara Cloud Services APIs which precisely define the permitted functionality.
Zadara Cloud Services Project Roles, which determine the type of user, who is permitted to perform this functionality. There are three types of users or roles: Member, Tenant Admin and Admin.
Each policy and API is typed according to the roles which are permitted to use them, generally speaking, reflecting the following:
Zadara Cloud Services policies consisting of APIs that create, view, modify and delete virtual resources belonging to projects to which the user has been assigned can be performed by all three roles, Member, Tenant Admin and Admin.
Zadara Cloud Services policies consisting of APIs which create and manage new projects and users within a specific account, assign users to these projects, and assign Zadara Cloud Services and AWS policies to these users, can be performed by only Tenant Admin and Admin users.
Zadara Cloud Services policies consisting of APIs which view, create, manage and remove physical resources, such as nodes (servers), disks, storage pools, physical networks, etc. can be assigned to and performed by only Admin users.
Each user is assigned per project, one or more Zadara Cloud Services Policies and a single Zadara Cloud Services Role. If the role of the user does not match the role type of any of the APIs included in the policy, then the user cannot perform these APIs, even if the policy which includes these APIs was assigned to the user.
Project Roles also determine the scope of the policies. When a policy is assigned to a specific project, the scope of this policy is dependent on the role, as follows:
Member - Policies apply only to the specific project to which they are assigned.
Tenant Admin - Policies apply to the entire account to which the specific project belongs. For example, if a Tenant Admin was assigned VMReadOnlyAccess for a specific project, the Tenant Admin user could see not only all of the VMs of that project, but also the VMs of all of the projects in the account to which the specific project assigned the policy, belongs.
Admin - Policies apply to the entire cluster. For example, if an Admin was assigned a VMFullAccess policy for a specific project, the Admin user could create VMs not only for that specific project, but for any project in any account in the entire cluster.
Zadara Cloud Services account roles are no longer relevant for determining which Zadara Cloud Services functionality is permitted by the user. They are used by the system only during login and in some future release they will be removed entirely from the Zadara Cloud Services GUI and API.
Whenever a new user is created via the GUI, a FullAccess policy is the suggested default Zadara Cloud Services policy. When a new user is created via the API/CLI, FullAccess is the automatically assigned Zadara Cloud Services policy. This policy provides full access to all of the services that each Zadara Cloud Services role granted in the past, prior to v5.3.4.
Zadara Cloud Services Policies and AWS API Policies In spite of the fact that AWS APIs and Zadara Cloud Services functionality overlap in many ways, they are in essence two independent areas of functionality, requiring separate sets of policies.
This supports the granting of access to one area without granting access to the other. For example, users working with only AWS APIs do not need access to the Zadara Cloud Services API/GUI.
The Zadara Cloud Services API is more extensive and all of its functionality is not covered by the AWS APIs.
Even APIs that appear to be similar in AWS API and Zadara Cloud Services API, such as “create vm” and “runinstances”, actually permit different actions.
Working with Zadara Cloud Services Policies¶
Zadara Cloud Services policies can be assigned while creating a user on the Permissions tab of the Create user wizard, or on the Manage Permissions dialog for an existing user.
Note
If a Zadara Cloud Services policy is assigned to a user while the user is in the middle of a session, it will not take effect until the user first logs out of the current session and then logs in again to a new session.
Assigning Legacy Zadara Cloud Services Role Permissions with Zadara Cloud Services Policies¶
In this page we will show how with Zadara Cloud Services policies, it is possible to create users with the same permissions granted by the legacy roles (prior to v5.3.4); Member, Tenant Admin, Admin and Read-only Admin.
Creating a user with the same permissions as the legacy Member.
Roles - Verify that it isMember(System default for Roles).
Policies - Verify that the FullAccess policy is selected (system default for Policies).
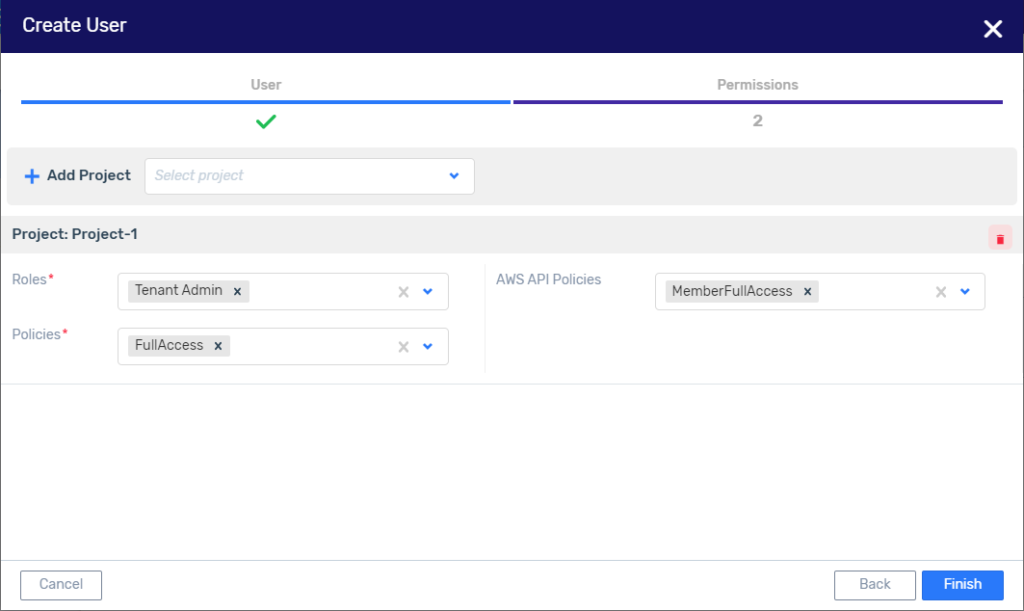
Creating a user with the same permissions as the legacy Tenant Admin.
Roles - ReplaceMemberwithTenant Admin.
Policies - Verify that the FullAccess policy is selected (system default for Policies).
Creating a user with the same permissions as the legacy Admin.
Roles - ReplaceMemberwithAdmin.
Policies - Verify that the FullAccess policy is selected (system default for Policies).
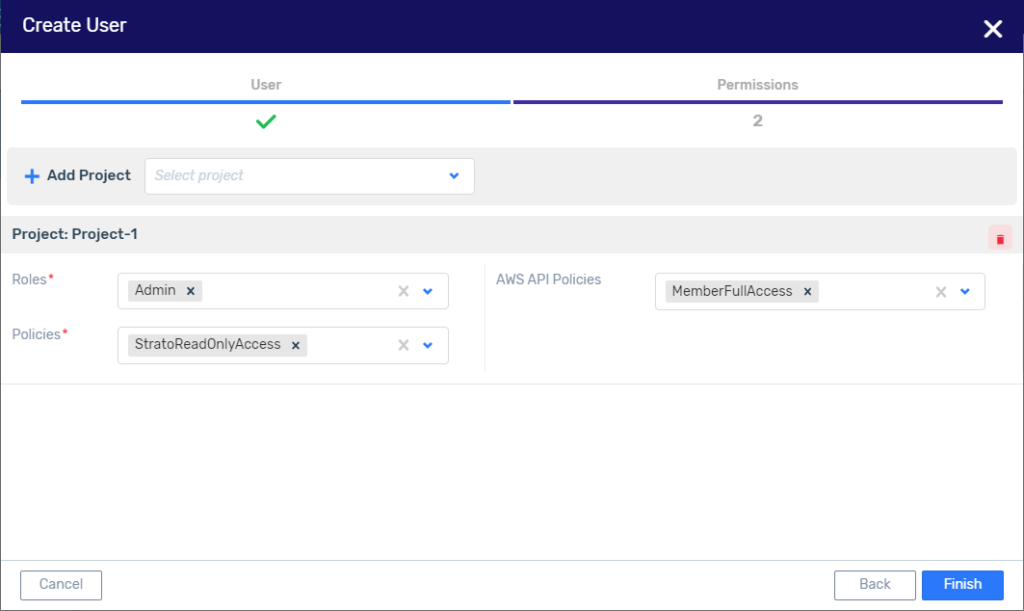
Creating a user with the same permissions as the legacy Read-Only Admin.
Roles - Replace Member with Admin.
Policies - Replace the FullAccess with the ZadaraReadOnlyAccess policy.
Assigning Permissions for Creating a VM¶
Here is an example of different ways to assign Zadara Cloud Services policies to grant the permissions needed by a user to create a VM.
A Member user with only VMFullAccess rights, cannot create a VM, as shown below: Although the VMFullAccess Zadara Cloud Services policy grants permission to create a VM and select an Instance Type, there are no permissions to view the following entities:
Image
Storage Pool
Subnet
A Member user with legacy permissions, which means full access to all Zadara Cloud Services member functionality, can create a VM. As shown below, all of the fields in the Create VM dialog, including, Image, Storage Pool and Subnet are available for Member users with legacy permissions.
A Member user assigned the VMFullAccess Zadara Cloud Services policy together with the ZadaraReadOnlyAccess policy can also create a VM.
The VMFullAccess Zadara Cloud Services policy permits the creation of a VM and the selection of any Instant Type.
The ZadaraReadOnlyAccess Zadara Cloud Services policy permits the viewing and selecting of any entity available to the legacy Member user, including the following:
Images
Storage Pools
Subnets
A Member user assigned the VMFullAccess Zadara Cloud Services policy together with the following three read-only Zadara Cloud Services policies can also create a VM:
The VMFullAccess Zadara Cloud Services policy permits the creation of a VM and the selection of an Instant Type.
The ImagesReadOnlyAccess Zadara Cloud Services policy permits the viewing and selecting of Images.
The StorageReadOnlyAccess Zadara Cloud Services policy permits the viewing and selecting of Storage Pools.
The VPCReadOnlyAccess Zadara Cloud Services policy permits the viewing and selecting of Subnets.
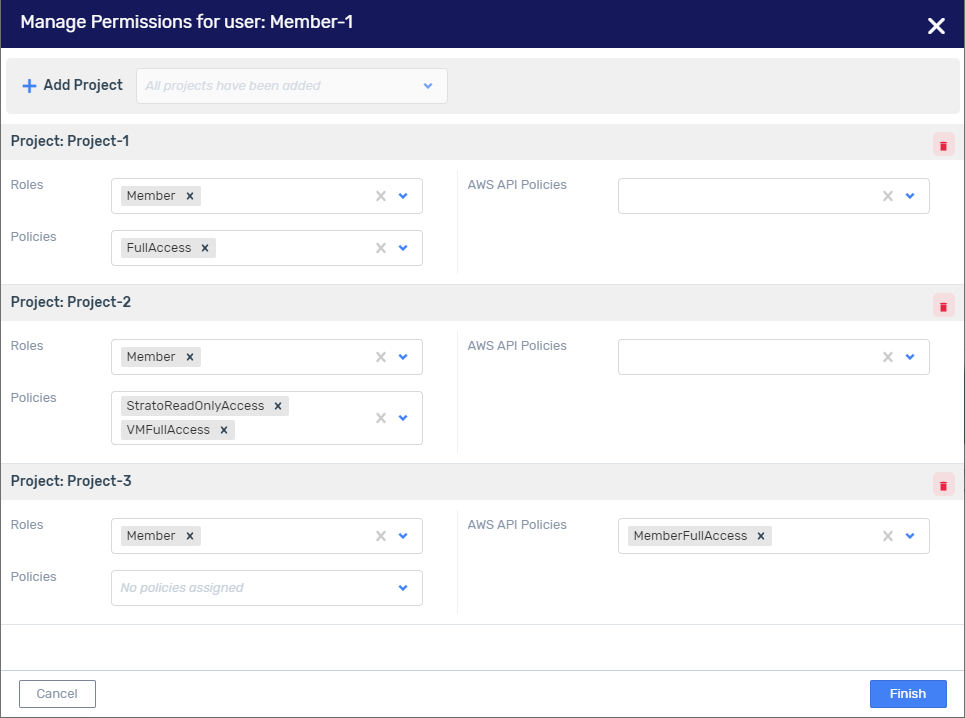
Assigning Permissions for Multiple Projects to a Single User¶
Here is how you can assign multiple projects to a single user. This can be done when creating the user or by Managing the Permissions of an existing user. For example, if you want to assign permissions for only Zadara Cloud Services functionality (but not AWS API functionality) for each of three different projects as follows:
Project-1 - Full legacy Member role permissions
Project-2 - Permissions to create VMs and many other actions concerning VMs
Project-3 - To be determined
In the Manage Permissions for user window, the following information needs to be applied:
Roles - Verify that the same single role,Member, has been assigned to each project.
Note
It is strongly recommended not to assign to the same user, different roles for different projects.
Policies- Each Project should be assigned the following Zadara Cloud Services policies:
Project-1 - Select the
FullAccesspolicyto grant Member legacy permissions.Project-2 - Select the
VMFullAccessandStratoReadOnlyAccessto grant permissions to create a VM, including viewing Images, Storage Pools and Subnets, access to which is necessary when creating a VM.Project-3 - Leave empty until User-1’s responsibilities vis a vis this project have been determined.
Note
As long as at least one project has both assigned a Zadara Cloud Services Role and Policy, the user’s permissions for other projects need not be completely defined.
AWS API policies- Empty theMemberFullAccesspolicy from each of the projects.
Finish- Click Finish.
List of Managed Zadara Cloud Services Policies¶
Zadara Cloud Services Policies consist of basically two policies per service, one for FullAccess of all the service’s APIs, and one for ReadOnly access of all the service’s APIs. Exceptions to this rule are:
The Identity Service which has two additional policies:
IdentityBasicUsage - which provides access to those identity entities available to a Member user.
IdentitySTSAssumeRole - which provides the ability to obtain an IAM role using the ‘assume-role’ API
The Snapshot service which has three sets of FullAccess and Zadara ReadOnlyAcces policies, one set for each of the following:
Snapshot
RemoteSnapshot
RemoteVMSnapshot
The VM service which has two sets of FullAccess and ZadaraReadOnlyAcces policies, one set for each of the following:
VM
VMSnapshot
FullAccess – a policy which provides full access to all Zadara Cloud Services APIs based on the user’s role
ZadaraReadOnlyAccess - a policy which provides read-only access to all Zadara Cloud Services APIs based on the user’s role. (A user with an admin role and this Zadara Cloud Services policy will have the same permissions as the legacy user with a Read-only admin role.)
Below is a list of all Zadara Cloud Services Policies with their descriptions and the roles for which they are enforced. To see the actual content of a policy go to the Identity & Access > Zadara Cloud Services Policies view, and click on the requested policy.
Zadara Cloud Services Policy |
Description |
Available to: |
|
|---|---|---|---|
AutoScalingFullAccess |
Provides full access to all autoscaling-group APIs |
All 3 roles |
|
AutoScalingReadOnlyAccess |
Provides read-only access to all autoscaling-group APIs |
All 3 roles |
|
CRSFullAccess |
Provides full access to all container registry APIs |
All 3 roles |
|
CRSReadOnlyAccess |
Provides read-only access to all container registry APIs |
All 3 roles |
|
CertificateManagerFullAccess |
Provides full access to all certificate APIs |
All 3 roles |
|
CertificateManagerReadOnlyAccess |
Provides read-only access to all certificate APIs |
All 3 roles |
|
CloudWatchFullAccess |
Provides full access to all cloudwatch APIs |
All 3 roles |
|
CloudWatchReadOnlyAccess |
Provides read-only access to all cloudwatch APIs |
All 3 roles |
|
ConversionsFullAccess |
Provides full access to all conversion APIs |
All 3 roles |
|
ConversionsReadOnlyAccess |
Provides read-only access to all conversion APIs |
All 3 roles |
|
DBCFullAccess |
Provides full access to all DB cluster APIs |
All 3 roles |
|
DBCReadOnlyAccess |
Provides read-only access to all DB cluster APIs |
All 3 roles |
|
DBSFullAccess |
Provides full access to all DB APIs |
All 3 roles |
|
DBSReadOnlyAccess |
Provides read-only access to all DB APIs |
All 3 roles |
|
EngineFullAccess |
Provides full access to all engine APIs |
All 3 roles |
|
EngineReadOnlyAccess |
Provides read-only access to all engine APIs |
All 3 roles |
|
ExternalEndpointFullAccess |
Provides full access to all external-endpoint APIs |
All 3 roles |
|
ExternalEndpointReadOnlyAccess |
Provides read-only access to all external-endpoint APIs |
All 3 roles |
|
FullAccess |
Provides full access to all Zadara Cloud Services APIs based on user’s scope |
All 3 roles |
|
GuestnetToolFullAccess |
Provides full access to all guestnet-admin-tool APIs |
All 3 roles |
|
GuestnetToolReadOnlyAccess |
Provides read-only access to all guestnet-admin-tool APIs |
All 3 roles |
|
HotUpgradeFullAccess |
Provides full access to all hot-upgrade APIs |
Admin |
|
HotUpgradeReadOnlyAccess |
Provides read-only access to all hot-upgrade APIs |
Admin |
|
IdentityBasicUsage |
Provides access to basic identity entities operations. |
All 3 roles |
|
IdentityFullAccess |
Provides full access to identity APIs |
Tenant Admin, Admin |
|
IdentityReadOnlyAccess |
Provides read-only access to identity APIs |
All 3 roles |
|
IdentitySTSAssumeRole |
Provides the ability to obtain an IAM role using the ‘assume-role’ API |
All 3 roles |
|
ImagesFullAccess |
Provides full access to all image APIs |
All 3 roles |
|
ImagesReadOnlyAccess |
Provides read-only access to all image APIs |
All 3 roles |
|
InspectorFullAccess |
Provides full access to all inspector APIs |
Admin |
|
InspectorReadOnlyAccess |
Provides read-only access to all inspector APIs |
Admin |
|
KubernetesFullAccess |
Provides full access to all Kubernetes APIs |
All 3 roles |
|
KubernetesReadOnlyAccess |
Provides read-only access to all Kubernetes APIs |
All 3 roles |
|
LbaasFullAccess |
Provides full access to all LBaaS APIs |
All 3 roles |
|
LbaasReadOnlyAccess |
Provides read-only access to all LBaaS APIs |
All 3 roles |
|
MapReduceFullAccess |
Provides full access to all map-reduce APIs |
All 3 roles |
|
MapReduceReadOnlyAccess |
Provides read-only access to all map-reduce APIs |
All 3 roles |
|
NFSFullAccess |
Provides full access to all NFS APIs |
All 3 roles |
|
NFSReadOnlyAccess |
Provides read-only access to all NFS APIs |
All 3 roles |
|
NodesFullAccess |
Provides full access to all node APIs |
Admin |
|
NodesReadOnlyAccess |
Provides read-only access to all node APIs |
Admin |
|
ObjectStoresFullAccess |
Provides full access to all object-store APIs |
All 3 roles |
|
ObjectStoresReadOnlyAccess |
Provides read-only access to all object-store APIs |
All 3 roles |
|
ProtectionFullAccess |
Provides full access to all protection APIs |
All 3 roles |
|
ProtectionReadOnlyAccess |
Provides read-only access to all protection APIs |
All 3 roles |
|
QuotasFullAccess |
Provides full access to all quota APIs |
All 3 roles |
|
QuotasReadOnlyAccess |
Provides read-only access to all quota APIs |
All 3 roles |
|
RemoteSnapshotFullAccess |
Provides full access to all remote-snapshot APIs |
All 3 roles |
|
RemoteSnapshotReadOnlyAccess |
Provides read-only access to all remote-snapshotAPIs |
All 3 roles |
|
RemoteVMSnapshotFullAccess |
Provides full access to remote VM Snapshot APIs |
All 3 roles |
|
RemoteVMSnapshotReadOnlyAccess |
Provides read-only access to remote VM Snapshot APIs |
All 3 roles |
|
Route53FullAccess |
Provides full access to all Route53 APIs |
All 3 roles |
|
Route53ReadOnlyAccess |
Provides read-only access to all Route53 APIs |
All 3 roles |
|
SnapshotFullAccess |
Provides full access to all local compute-snapshot APIs |
All 3 roles |
|
SnapshotReadOnlyAccess |
Provides read-only access to all local compute-snapshot APIs |
All 3 roles |
|
StorageFullAccess |
Provides full access to all storage APIs |
Admin |
|
StorageReadOnlyAccess |
Provides read-only access to all storage APIs |
All 3 roles |
|
StratoReadOnlyAccess |
Provides read-only access to all Zadara Cloud Services APIs based on user’s scope |
All 3 roles |
|
VMFullAccess |
Provides full access to VM APIs |
All 3 roles |
|
VMReadOnlyAccess |
Provides read-only access to VM APIs |
All 3 roles |
|
VMSnapshotFullAccess |
Provides full access to VM Snapshot APIs |
All 3 roles |
|
VMSnapshotReadOnlyAccess |
Provides read-only access to VM Snapshot APIs |
All 3 roles |
|
VPCFullAccess |
Provides full access to all VPC APIs |
All 3 roles |
|
VPCReadOnlyAccess |
Provides read-only access to all VPC APIs |
All 3 roles |
|
VolumesFullAccess |
Provides full access to all volume APIs |
All 3 roles |
|
VolumesReadOnlyAccess |
Provides read-only access to all volume APIs |
All 3 roles |
Note
It is currently possible to assign a Zadara Cloud Services policy to a user, for whose role, the APIs in this policy will not be permitted. For example, it is possible to assign the NodesFullAccess policy to Member users, even though the APIs in this policy will not be permitted for Members, but only for Admins. In some future release, this invalid assignment will be prevented.
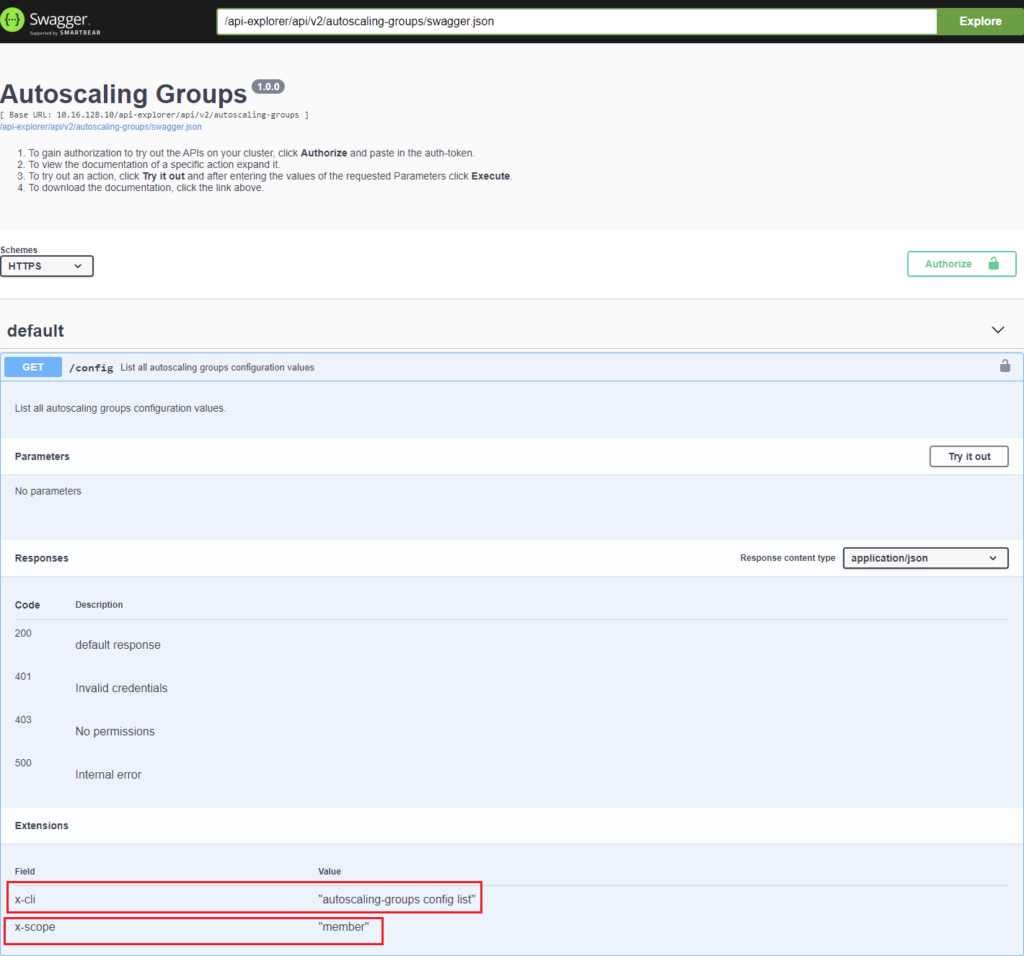
A Zadara Cloud Services policy which is permitted for a Member or Tenant Admin role, may nevertheless include some APIs/CLIs which are not permitted for that role. For example, the VMFullAccess policy whose APIs/CLIs are permitted for all 3 roles, including the Member role, contains the API, ‘vm live-migrate’ which migrates VMs from one node to another. This action can be performed only by an Admin user. To determine the role for which specific APIs of a Zadara Cloud Services policy are permitted, access the API Explorer for the service covered by the policy and open the API, as shown below.
In the Extensions section at the bottom of the window, the x-cli field displays the name of the CLI while the x-scope field displays the role with the least amount of permissions which may use this CLI. (‘member’ has less permissions than ‘tenant_admin’ which has less permissions than ‘admin’. If x-scope = ‘all’ permissions are not required to perform the CLI.)