Zadara Cloud Services Catalog¶
Cloud Services Administration¶
Each customer that orders Cloud Services from the Zadara Provisioning Portal, gets an account on a specific cloud in the requested location. The account contains one Project by default, but additional projects can be created. A Project is a container of resources (VPCs, VMs, ELB, etc…) to separate different application groups or environments. A Project is similar to an AWS project, or VMware folder. The Tenant Admin can assign to users, per project, roles and policies.
Users and Roles¶
On Zadara IaaS platform users are defined with one of the following roles:
Account Member¶
This role allows the user to use the console, policies and APIs for creating, viewing, modifying and deleting virtual resources (e.g. VMs, Volumes, etc…) belonging to projects to which the user has been assigned. This is the standard role for most users.
Tenant Admin (Account Admin)¶
In addition to allowing the use all functions which are granted to a Member, the Tenant Admin role also allows the user to use policies and APIs for creating and managing new projects and users within a specific account. The user that is registered on the Zadara Provisioning Portal for Compute services, has the role of Tenant Admin and is responsible to manage the account on behalf of her organization. The Tenant Admin can create additional users with this role.
Cloud Admin¶
In addition to allowing the use all functions which are granted to a member and Tenant Admin, the Cloud Admin role also allows the user to use policies and APIs for viewing, creating, managing and deleting all physical resources, such as compute nodes, disks, storage pools, physical networks, etc., and administrative entities such as accounts. It is possible to create more than one user per region with Cloud Admin rights. Typically this role is kept by Zadara Operations team, or by the MSP who owns a specific cloud deployment.
The following services are available for regular users (account members):
Compute¶
Compute Instances (VMs)¶
You can create Virtual Machines of any type (built-in or user defined), based on OS image, over a cloud-optimized hypervisor (Enhanced KVM). This service has AWS EC2 compatible API that offers standard AWS API for application integration
Snapshots¶
A snapshot is a copy of the volumes of a virtual machine at a given point in time. Snapshots provide a change log for the volume and are used to restore a VM to a particular point in time when a failure or system error occurs. You can create snapshots of the VMs that are in the system, and use these snapshots to restore any VM if needed
Key Pairs (security keys settings)¶
Public–key cryptography is used to encrypt and decrypt login information for linux instances.. (Instances created from a Windows image are accessed by a password instead.) A public key is used to encrypt a piece of data, and then the recipient uses the private key to decrypt the data. These two keys are known as a key pair. Key pairs enable you to securely access your instances using a private key instead of a password.
Auto Scaling¶
The system monitors applications and automatically adjusts allocated resources to meet evolving requirements. It simplifies scaling operations to a minimal effort based on a simple and powerful interface for planning and defining launch configurations and scaling policies. You define the policy, and the system ensures performance and availability while keeping resource utilization optimized to reduce costs.
Networking¶
VPC¶
The Virtual Public Cloud (VPC) is your own private data center within the cloud infrastructure. You get to decide the network addresses that you will use throughout your infrastructure. Since this is your network, you can decide to slice it up any way you prefer. The VPC is a networking resource with a logical router at its core. When you create a VPC you specify a CIDR block. All subnets that you will create in the VPC will be carved out from this CIDR block, and. the router will ensure IP connectivity between them.
Subnets¶
Subnets are the next piece of the VPC. There are a number of reasons to use different subnets in your VPC and not simply leave everything in one big network, such as: segregation between private and public facing networks, availability zones.
Network Interfaces¶
A virtual network interface (VIF) is an abstract virtualized representation of a computer network interface. Each virtual machine (VM) may have one or more virtual network interfaces that act as virtual NICs.
Route Tables¶
The basic tenet of networking is that everything inside your subnet stays inside your subnet – and if you want to go outside of your subnet, you need to go through the default gateway and from there be routed to get to your destination network. The route tables are associated with each of your subnets to allow the flow of traffic according to the policies and options you have in place.
Internet Gateways (IGW)¶
Your connection to the outside world is the Internet Gateway. Having instances running in a cloud is great, but if you cannot get to them from the outside world they might be useless. Manageability is going to be very challenging – if not completely impossible.
Elastic IP (EIP)¶
Elastic IPs are used to expose instances outside of the Zadara compute cloud. An EIP will be used in the network address operation (NAT) of all traffic to/from the virtual network interface with which it is associated.
VPC Peering (in the same cluster)¶
VPC peering lets you create direct IP connectivity between any two VPCs. Direct connectivity between VPCs means that servers in a VPC can be reached from the other VPC without the need for floating IPs or traffic flowing through external routing. VPC peering is simply L3 connectivity realized using routing tables and IP connectivity.
NAT Gateways (NGW)¶
There will be cases where you don’t want instances to be exposed to the outside world and you don’t want them to have public IP addresses. However, these instances may still need access to the outside world to get updates or to send information. By using a NGW, you can allow outbound access to the internet and limit the inbound access to those instances, providing an additional layer of abstraction and protection for your workloads.
DNS¶
The DNS Service provides an easy-to-manage DNS solution for your private networks. It offers high availability and a cost-effective way to connect applications and services and make them available to users. The DNS service is seamlessly integrated with the resources and services of the cloud. You can map domain names to your compute instances and other services.
Security Groups¶
Security groups are applied to the virtual network interfaces to control the inbound and outbound traffic. They are whitelists. Traffic that does not match any rule in the security group will be discarded.
For each security group, you include one set of rules that controls the inbound traffic to the instances, and a separate set of rules that controls the outbound traffic from the instances.
Storage¶
Block Volumes (EBS)¶
Native block storage, designed to be extremely scalable, agile and flexible, while fully compatible with the requirements of cloud computing. The Block Storage service offers comprehensive block storage capabilities, enabling you to reduce latency and overhead and to increase throughput. The service is based on Zadara VPSA block services and fully compatible with AWS EBS API for application integration.
File Shares¶
NAS service is available to provide scalable files shares via NFS or SMB protocols. The service is based upon the Zadara VPSA NAS offering that allows file access to all associated VM instances. (This service is currently provisioned via the Zadara VPSA interface, and is not compatible with AWS EFS API)
Object Storage¶
Both private and public object storage services are available on the Zadara IaaS platform. You can create your own private Object Storage, where you have full control, or just get an account on a Zadara regional public service. Both can be accessed via AWS S3 API, or Swift interface. A private Object Storage is directly connected to your VPC, while the public Object storage is accessible via a public IP. (This service is currently provisioned via the Zadara Object Storage interface)
Load Balancing¶
Load Balancers¶
The Managed Load Balancers service offers the ability to spin up, customize and scale load balancers to support fault tolerance and ensure high availability and application scalability over time. To simplify operations even further, this service supports AWS ELB APIs. It routes traffic according to application or network considerations and provides the required amount of load balancing capacity needed and distributes it to meet high availability and network performance requirements.
Target Groups¶
A target group is a group of instances to which a load balancer directs application traffic. The instances in this group collectively do the processing work that the application requires.
Machine Images¶
Images¶
The system comes with a number of VM images ready to use. In addition you can create your own images, as needed. Two image formats are supported - VMware OVA image and the KVM compatible image in RAW or QCOW2 formats. The latter means that most OpenStack KVM images can be uploaded easily. All of the above are converted into the RAW format and preserved in the image repository in the cluster.
Images marketplace¶
Machine images of the different OSs can be downloaded from the Images market place, and be used to create Instances. For OSs that require activation (and vendor fees) you will need to get the activation codes directly from the vendor.
Monitoring¶
Events¶
Zadara compute cloud provides information about various events in your system. Events are any actual changes or attempts at changes in the state of the services, whether initiated manually or automatically by the system. This service provides an events viewer with the ability to filter by date, severity, time, etc…
The system offers visualized metrics, logs and events of all resources, including CPU utilization, memory, storage and network usage. Insights are available on a broad system view, as well as on a per-instance and per-volume view, to quickly and effectively resolve issues from diagnostics to understanding the root cause.
You can configure the system events to be sent to a remote syslogs/logstash server located at some external endpoint.
Alerts¶
The cloud’s automated monitoring helps you focus on proactively solving problems, rather than wasting time to identify them. You can set alarms on all relevant metrics and deeply reduce time to response and facilitating automation. You can easily configure your set of metrics-based alarms, using multiple conditions, to notify you on threshold crossing. You will receive your alerts in real-time.
Certificates¶
Certificates¶
To secure your cloud domain name you need to procure an SSL Certificate from a trusted SSL Certificate Authority and install it on your domain. Once you get the certificate file from the CA, this service allows you to apply the certificate to the system.
Protection¶
Groups (policies)¶
The Protection Group basically consists of a schedule for automatic local backup of a project. It is a backup policy that defines the backup window, recurring schedule, and its retention period.
In addition to the member services the following services are available for Tenant Admins:
Monitoring¶
System Alerts¶
The account admin and define Alerts related to the account, and receive alerts notification based on the account situation, and system health.
Identity and Access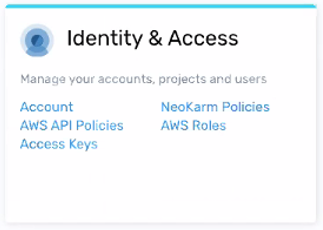 ¶
¶
Account¶
Ability to monitor and modify the account state, create and manage projects within the account, and the ability to manage member users and their access rights.
Access Keys¶
You have to pass in account-specific credentials that authenticate you as a valid user, before you can access the system. For example, to access the GUI or Management console, you sign in with a username and password. Similarly, for programmatic access, you pass in an access key and a secret key. As the API’s are AWS compatible the authentication mechanism is also identical.
AWS Roles¶
IAM Roles are policy-based tokens with temporary credentials allowing a user temporary access, to AWS services and actions which the user is normally not permitted to access. These users may be from different projects or even different accounts. These roles can also be embedded into specific instances allowing these instances access to the necessary actions.
The IAM roles are independent of the three roles discussed above: Cloud Admin, Tenant Admin and Member.
AWS API Policies¶
Usage of all AWS compatible services and actions are governed by their corresponding AWS-managed policies.These policies can be assigned per project to Users, Groups of users and STS Roles. System usage is governed by NK policies together with the three roles: Admin, Tenant Admin and Member.
Zadara Cloud Services API Policies¶
Note
This section is under development.